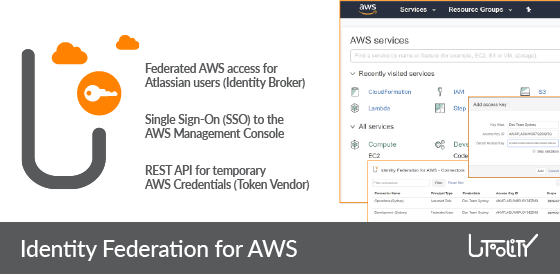
Single sign-on (SSO) to AWS resources – empower your teams with seamless Amazon Web Services access and integrate AWS into your Jira and Bamboo DevOps workflows:
- Empower your Atlassian users – provide single sign-on (SSO) enabled links to the AWS Management Console from the AWS Resources menu and the AWS CodeCommit web repository viewer
- Share your AWS resources – use the AWS Resource link to reference resources from Jira issues
- Secure your AWS credentials – store long-term AWS security credentials with industry standard encryption without exposing them to users or apps, use the AWS Security Credentials dialog to provide temporary credentials to other tools and services for the duration of your work day, and use the AWS Security Credentials task and Amazon ECR Authentication Credentials task (Docker) to provide variables with temporary credentials to AWS unaware tasks in Bamboo
- Relieve your AWS administrators – forget about distributing or revoking AWS credentials and never worry about team composition or employee leave: AWS access follows group membership once you grant fine-grained permissions via IAM policies
- Integrate your Atlassian apps – use the REST API to grant users SSO enabled access to AWS resources